The RealVNC Blog
Welcome to our blog. Discover the latest information about remote access, how-to guides, and a glimpse of everything we are up to!
Latest articles
Episode 4 of the Remote Access Redefined Podcast is here. And what topic is more important than security? Which is...
Open-source VNC software can be a great starting point. It’s free, flexible, and widely available. For teams building proofs of...
The world’s original remote access solution will be at Smart Manufacturing Week 2025, at NEC Birmingham, Smart Factory Expo –...
Open-source VNC software can be a great starting point. It’s free, flexible, and widely available. For teams building proofs of...
The world’s original remote access solution will be at Smart Manufacturing Week 2025, at NEC Birmingham, Smart Factory Expo –...
Product Tutorial
A Direct Connection is something that users in highly secured environments will want to use. This makes sure that none...

Experience the Next Chapter in Remote Access—Watch Now
Watch our exclusive on-demand webinar and explore the latest advancements in RealVNC Connect v8. This transformative update introduces a redesigned user interface, enhanced usability, and powerful new features designed for modern IT professionals.
Raspberry Pi Tutorial
Introduction to Raspberry Pi Remote Access This article applies to RealVNC Connect through version 7. There’s nothing more frustrating than...
Experience the Next Chapter in Remote Access—Watch Now
Watch our exclusive on-demand webinar and explore the latest advancements in RealVNC Connect v8. This transformative update introduces a redesigned user interface, enhanced usability, and powerful new features designed for modern IT professionals.
General Tutorial
A Direct Connection is something that users in highly secured environments will want to use. This makes sure that none...
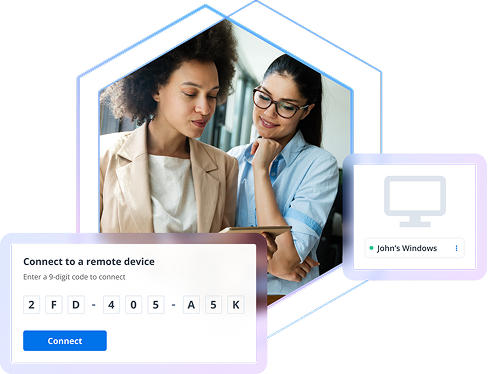
Ever tried to connect to a remote device but was asked for a remote access code? This secure method acts...
Ever tried to connect to a remote device but was asked for a remote access code? This secure method acts...
Remote Access
Open-source VNC software can be a great starting point. It’s free, flexible, and widely available. For teams building proofs of...
Some tasks in digital workflows are deceptively simple until scale, compliance, or security enter the picture. Screen sharing is one...
Open-source VNC software can be a great starting point. It’s free, flexible, and widely available. For teams building proofs of...
Some tasks in digital workflows are deceptively simple until scale, compliance, or security enter the picture. Screen sharing is one...
This is the second article in our series concerning remote access integration security in healthcare equipment manufacturing. We’ll be discussing...
Remote Desktop
Top 7 Best VNC Viewers for Mac in 2025 If you’re looking for the best VNC viewers for Mac, hear...
While macOS only enjoys 16% of the desktop OS market share, it’s still the most popular choice for many developers,...
While macOS only enjoys 16% of the desktop OS market share, it’s still the most popular choice for many developers,...
Compare & Contrast
Is it better to host your remote access infrastructure yourself or rely on cloud-based services? Businesses today face a critical...
As remote work becomes a long-term standard, every business needs effective ways to maintain secure, productive workflows. For this reason,...
Remote desktop technologies are essential tools for modern businesses, enabling seamless remote work, efficient support, and effective collaboration. Two common...
As remote work becomes a long-term standard, every business needs effective ways to maintain secure, productive workflows. For this reason,...
Remote desktop technologies are essential tools for modern businesses, enabling seamless remote work, efficient support, and effective collaboration. Two common...
Remote Support
High-quality remote support is as much about convenience as it is about security, so IT teams can perform at their...
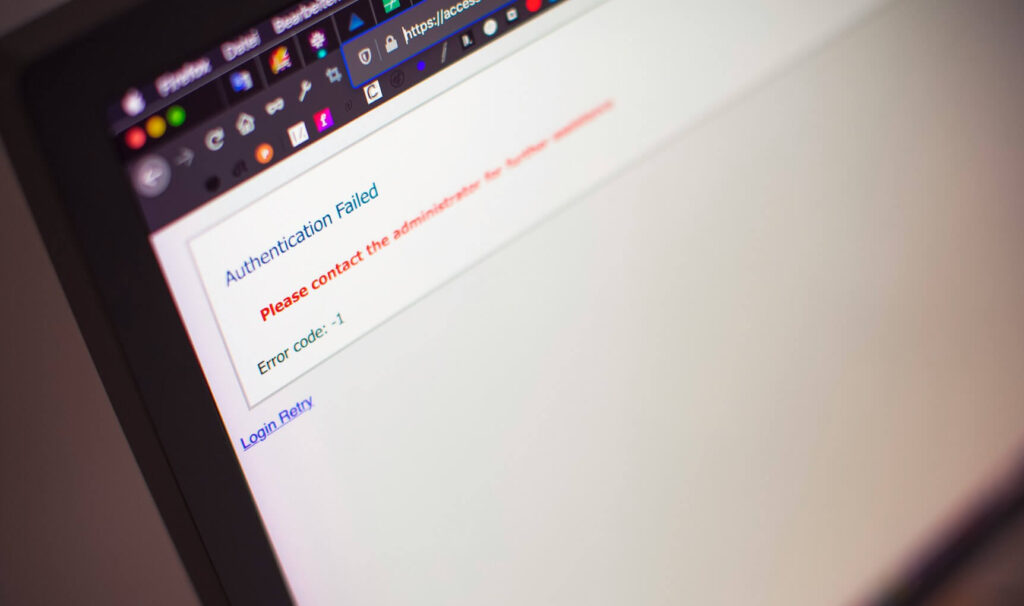
Security and Privacy
Try RealVNC® Connect today for free
We don’t require credit card data. 14 days of free, secure and fast access to your devices. Upgrade or cancel anytime