What follows is a look at secure remote access and its benefits. We’ll be checking out different aspects, as follows:
- What is remote access?
- Why is remote access security important?
- How to secure remote access
- Secure remote access solutions
- What are some remote access security best practices?
So, without further ado, let’s sink our teeth into the essentials of secure remote access.
What is remote access?
A question that’s as old as the world. Well, maybe not as old as the world, but definitely as old as RealVNC. And that’s because we’re talking about the company that invented the VNC protocol.
So, let’s look at what remote access is. A simple definition would be “software that allows its user to use a remote computer and perform tasks on it as if they were sitting in front of it”. Desktop sharing software is another term that’s used for remote access.
Said tasks can range from actually using the computer to transferring files to and from it or locally printing documents from it.
What are the benefits of remote access?
This question has many answers, and they also depend on the field you’re working in. Here are some of them:
- Flexibility – users can work and access resources from virtually anywhere, provided they have an internet connection.
- Productivity – users can perform tasks instantly.
- Lower costs – most issues can be resolved remotely, so travel and other costs are eliminated.
- Less or no office space – remote access makes working from home an option, so keeping permanent offices is no longer necessary.
- Smaller carbon footprint – with less travel comes a smaller carbon footprint for the organization.

Why is remote access security important?
When you choose a remote access provider, it’s like choosing someone to share the keys to your house with. You need to trust them, as all the information on your computer will be accessible to them. That’s why you need to be able to trust the secure remote access provider and its technology.
Remote access security is not a nice to have. It’s a must-have in today’s world, in a time when everything is stored on computers and smartphones.
We’ll look at what you need to ask your remote access provider for.
How to secure remote access
It’s not enough for a secure remote access solution to claim that it’s keeping your data safe. It has to offer some features that make sure said data doesn’t end up in the wrong hands. It also needs to be built with security in mind.
You shouldn’t need to trust the provider to be able to trust the solution itself. This means that data must be end-to-end encrypted. Also, every connection needs to be treated by the secure remote access software as if it’s made in a hostile environment. Furthermore, the owner of the computer must be the one deciding who gets to connect and who doesn’t.
To ensure security, multifactor authentication is an absolute must. And so is device sign-in verification; namely, your secure remote access solution telling you when a new device connects.
Finally, you shouldn’t take what your software provider says for granted. The fact that they claim that their solution is secure doesn’t mean it is. They have to be able to prove it, in the form of an independent white box security audit from a reputable provider.
Secure remote access solutions
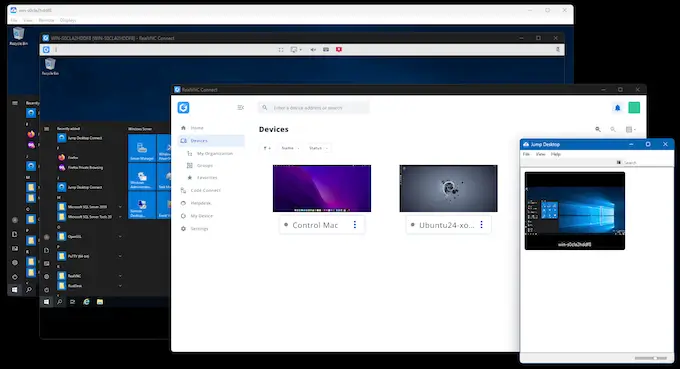
RealVNC’s remote access solution, RealVNC Connect, offers all the above and more. It’s a multiplatform secure remote access solution which allows you to use your devices as if you were sitting in front of them.
RealVNC Connect runs on Windows, Mac, Linux, as well as Android and iOS mobile devices, and it also comes preinstalled on Raspberry Pi. All connections are encrypted, and the software is fully configurable out of the box. It also provides vigorous security options and authentication tools, giving you complete control.
What are some remote access best security practices?
Now that you know all the above, do you want to make sure that your use of remote access is as secure as possible? A number of remote access security best practices will need to be in place in order for this to be possible.
As a business that wants to build digital trust, you’ll need to make sure that strict policies are in place across your organization.
List of remote access best practices
Here are some of the best practices to implement across your business when it comes to staying safe with remote access:
Multifactor authentication – implemented wherever possible.
Clear policies – make sure that everyone understands your policies, and that they are correctly implemented.
A strong password policy – make sure that everyone uses strong passwords, which they change regularly.
Cloud-brokered connections – use these if the network is not a private one.
Access control – your remote access solution needs to offer a robust way of controlling who is allowed to connect to what.
Secure remote access software with proven security – use a solution that can back its claims. This means being able to show an up-to-date security audit.
With that said, why don’t you go ahead and try a truly secure remote access solution? VNC Connect offers a free 14-day trial; click below to get yours!