With just slightly under two-thirds of U.S. employees working remotely at least part-time, the focus for threat actors has been to shift to obtaining valid credentials. This may be the result of a few factors that cybercriminals are benefitting from:
- It’s the lowest hanging “fruit” for a cyberattack – The obtaining of a user’s credentials is a simple matter of creating some urgency within a phishing attack and convincing the victim that they need to log onto, say, Microsoft 365, in order to see the relevant attachment, link, etc. using an impersonated logon page that actually just captures credentials.
- Credentials provide access to cloud and on-prem resources. With the majority of organizations using Microsoft 365 and a majority of those syncing credentials to their on-premises Active Directory, the same credential could be used as part of a hybrid attack that spans cloud-based applications, services, and data, as well as entrée to internal resources once remote access is established.
- Credentials are a Dark Web commodity – Some threat actor is buying valid compromised credentials at any given moment somewhere on the Dark Web that allows access to an RDP session, a compromised corporate endpoint, or a cloud-based platform.
The reality today is that there’s a need to no longer assume that the user of a credential is actually the owner of the credential. Multi-Factor Authentication (MFA) will assist in verifying this, but there are far too many cases of “MFA fatigue” where threat actors continue to prompt the credential owner repeatedly after business hours in order to get them to respond to an MFA request just to get the requests to stop (with the threat actor gaining access).
So, what does all this have to do with session recording?
In a world where remote access is still used today to provide legitimate access to internal corporate resources to external users, as well as facilitate access to remote resources by users already logically residing within the corporate network, it’s no longer a given that just because someone authenticated as a specific user, it’s actually them – in other words, an external threat actor with control of a credential. On the other hand, don’t forget insider threat actors who may be the credential owner but are no longer acting in a manner that benefits the organization.
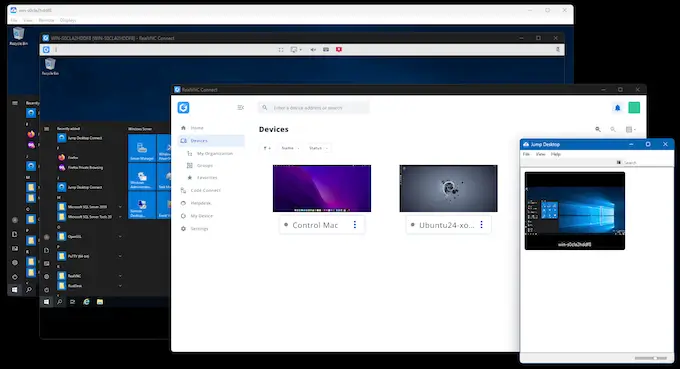
As an additional precaution to ensure a proper state of cybersecurity, it’s necessary for organizations to have the ability to record and review remote sessions to assess and determine the validity of the actions taken. While not all Remote Access solutions have a session recording functionality, it’s this capability that will facilitate a Security team’s review of suspect remote sessions. In practical use, there are three ways – listed below – that having replayable recordings of all remote access sessions can strengthen your organization’s cybersecurity stance.
Insight
Simply knowing that a given credential established a remote session to a certain endpoint is just a piece of information. There’s no intelligence there that determines whether the session is suspect (other than, perhaps, seeing that a session is established, say, well outside normal working hours – something the user never does). SIEM solutions tend to be the typical solution that will point this kind of thing out.
But even if you are made aware that there’s a suspect remote access session in progress, it’s only through playback of session recordings (or even session auditing, if your Remote Access solution supports it) that you can gain the proper insight into each and every action that was taken during the remote session.
Context
If you were told that a user copied 500 critical files to a cloud-based file-sharing platform, is that a problem? The correct answer is you don’t know. Without proper context – such as the user reading an email from their boss just before asking them to do it, or, conversely, the user downloading hacking tools and malware just before exfiltrating all the files – you can’t correctly judge the single action.
The playback of session recordings provides unequivocal evidence to be used to establish context; the actions are taken before and after an activity in question are what’s going to help determine whether you have a cybersecurity issue on your hands or not.
Incident Response
And with the context, you also can determine the impact and scope of any and all actions taken during the session, providing the needed details to establish the necessary incident response actions that need to be taken.
For example, if an external threat actor remotely accessed a desktop and used that to access a number of other endpoints via SMB shares, Active Directory via LDAP, and used a number of hacking tools in the process, the Security team member reviewing the session now has a much better idea of the actions taken, the systems affected, the services impacted, and – in most attacks today – the data stolen.
Your Cybersecurity Strategy Needs to Include Session Recording
Any solutions used within your cybersecurity strategy usually play into one or more of three parts of the strategy – prevent, detect, and respond. The goal of anything involved in detecting usually involves gathering as many insightful details as possible. And while remote access session recording most definitely is not a security solution, it does provide Security teams with valuable insight into threat actions taken and fits rather well as a toolset in the respond category.
So, as you consider ways to best leverage remote access, keep in mind this capability that takes the simple extending of productivity to remote users and crosses over the value to your cybersecurity initiatives with tons more context and detail than even the best SIEM can provide on its own.