You’d think by now that RDP exposed to the Internet would be dead – after all, it’s a known fact (if you’re paying attention at all) that RDP and Phishing remain deadlocked in a battle for supremacy as the top initial attack vector in ransomware attacks. And yet, even IT folks are leaving RDP sessions open (thinking that using an alternate port will somehow obfuscate the fact that the service is Windows’ Remote Desktop service.
What does “Venus” do?
According to Bleeping Computer, a new ransomware gang, known as “Venus”, has sprouted up since August of this year, focusing their attack efforts on exposed RDP sessions (and, no, the port doesn’t matter; the threat actors scan every port looking at the response to determine it’s an RDP connection). Once within the victim network, Venus attempts to terminate 39 processes that may lock files (thus, keeping them from being able to be encrypted), deletes event logs, kills the Shadow Volume copies, and disables Data Execution protection – all before beginning the encryption of your data.
What to keep in mind
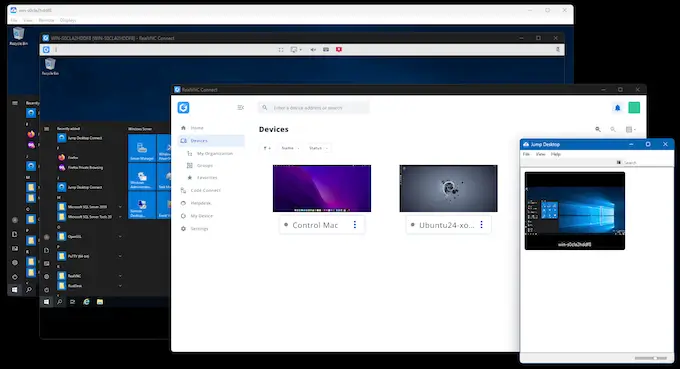
Organizations requiring any kind of remote access for their users should consider the use of remote access services that provide a number of security controls to ensure that, should a threat actor identify an Internet-facing remote service, they are unable to take advantage of the connection. The controls include:
- Support for multi-factor authentication – most RDP attacks are brute-force attacks, attempting password after password until they guess the right password. MFA nullifies this by requiring a secondary form of authentication.
- Support for Granular Restricted Access – RDP by default allows any user account that can authenticate (read: any account within Active Directory or within the endpoint’s local SAM database) to create a remote session. There are ways to limit who can use a given RDP session – using the Deny logon through Remote Desktop Service group policy, for example. But those organizations that need a more sophisticated ability to establish which accounts can access which desktops remotely may require a third-party remote access solution that provides a means to dictate this exactly in a way that aligns with business needs.
- In-Session Privilege Elevation – For those users that need elevated privileges, the privilege is usually found in the credential itself. So, should a threat actor guess the password to an account, they now have elevated privileges. The right remote access service should facilitate a connection for low-level users and provide an ability to elevate privileges for specific tasks or by making a separate request for an elevated session.
Venus ransomware is only the latest family to attack RDP. Organizations will only truly stop ransomware’s misuse of RDP when they kill the default Windows RDP service entirely and leverage something more mature, with both productivity and security in mind.