Whenever we talk about cyberattacks, there are three basic ways in which attackers gain access to a victim network:
Phishing: They use emails’ ability to logically infiltrate a network, potentially giving attackers a foothold should the attack be successful in infecting an endpoint.
Vulnerabilities: By using zero-day or known vulnerabilities (that have not been patched), attackers can gain elevated privileges on systems and applications and leverage them to access the rest of a network.
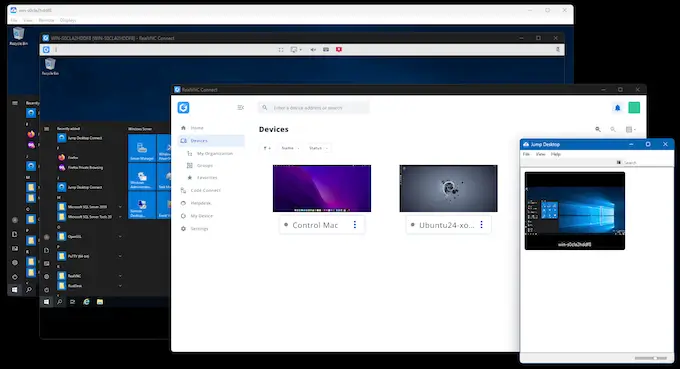
RDP/Remote Access: Attackers use either compromised credentials or brute force password attacks, using them as the conduit to gain entrance into a network.
Companies usually focus on the first two attack vectors above. When discussing the third, they usually focus on RDP itself rather than on how insecure the authentication is once an attacker jumps onto a remote logon session.
So, in this article, we want to explore what happens when an attacker finds and utilizes a remote access session (RDP or otherwise, herein generically referred to as remote access).
We’ll take a look at the brute force attack methods used to compromise a credential, how prevalent it is, why users are actually making it easy for the attacker, and what you can do about it.
What is a Brute Force Attack?
A brute force attack is a type of cyber attack where an attacker uses trial and error to guess or crack a user’s password, login credentials, or encryption keys. This attack method involves systematically trying all possible combinations of characters, numbers, and special characters to gain unauthorized access to a user’s account, system, or network.
Brute force attacks can be performed manually or using automated software tools, making them popular among hackers.
Types of Brute Force Attacks
There are several types of brute force attacks, including:
Simple Brute Force Attack: Involves trying all possible combinations of letters, numbers, and special characters to guess a user’s password.
Reverse Brute Force Attack: The attacker starts with a known password and tries to find a matching username.
Dictionary Attack: Attackers try a list of words, phrases, and common passwords to guess a user’s password.
Hybrid Brute Force Attack: This type of attack combines a dictionary attack with a traditional brute force attack.
Credential Stuffing: Involves using a list of stolen usernames and passwords to gain unauthorized access to multiple accounts.

Motives Behind Brute Force Attacks
Understanding the motives behind brute force attacks is essential for evaluating risks and implementing effective security measures. Cybercriminals rarely act without purpose. Their goals often include financial gain, espionage, or disrupting operations. For example, industries handling sensitive data, like healthcare or finance, face higher risks of espionage, while smaller businesses may be targeted for ransomware or credential theft due to limited IT budgets.
Here’s a closer look at why attackers employ brute force tactics:
Credentials Theft for Profit
One of the most common reasons behind brute force attacks is to steal user credentials, such as usernames and passwords. Once obtained, these credentials can be sold on dark web marketplaces, often as part of large data dumps, or used to gain unauthorized access to valuable systems. For instance, an attacker might sell login details to an organization’s internal systems, enabling others to launch targeted attacks like ransomware or data theft.
Ransomware Deployment
Brute force attacks are frequently used as an entry point for deploying ransomware. By gaining access to systems via compromised credentials, attackers can encrypt critical data and demand a ransom for its release. This motive has been amplified by the increase in remote work, which often relies on remote desktop protocols (RDP) or other remote access solutions that are vulnerable to brute force attacks.
Espionage and Data Extraction
Brute force attacks are used by cybercriminals with motives tied to corporate or state-sponsored espionage. They allow attackers to infiltrate networks and extract sensitive data. Attackers can target intellectual property, trade secrets, or classified information. They use weak authentication methods to access high-value systems.

System Disruption
Sometimes, the goal isn’t to steal data or money but to disrupt an organization’s operations. Brute force attacks can be a part of larger campaigns to overload systems, cause downtime, or erode customer trust. In these cases, the attackers aim to damage an organization’s reputation or capabilities rather than derive direct financial benefit.
Testing and Exploiting Security Weaknesses
Brute force attacks often serve as reconnaissance tools. Attackers may use them to probe an organization’s defenses, identifying weak points in authentication systems. This information can then be used to craft more sophisticated and targeted attacks.
Credential Reuse Across Platforms
Many people reuse passwords across multiple accounts. Knowing this, cybercriminals exploit brute force attacks to access not only one account but potentially an entire network of interconnected services. This tactic, known as credential stuffing, is especially problematic when a single compromised password can lead to broader breaches.
Initial Access Brokering
In some cases, brute force attacks are conducted by initial access brokers, cybercriminals who specialize in breaking into networks and selling access to other attackers. These brokers use weak authentication systems to gain entry and sell credentials to those looking to carry out large-scale attacks like espionage or ransomware.
Understanding these objectives can help organizations prioritize their defenses, such as enhanced authentication, routine security audits, and employee training, to mitigate vulnerabilities effectively.
Online and Offline Brute Force Attacks
Brute force attacks fall into two main categories: online and offline, each posing unique challenges.
Online Brute Force Attacks
These attacks target live systems or networks. Attackers repeatedly guess passwords using automated tools. They occur in real time, making them detectable by monitoring for unusual login attempts, such as repeated failures from a single IP address.
Mitigation strategies include rate limiting to slow attempts, CAPTCHA challenges to block bots, and multi-factor authentication (MFA) to enhance security.
Offline Brute Force Attacks
Offline attacks involve cracking stolen password hashes without interacting with live systems. Attackers use powerful tools to test combinations, making detection difficult.
Defense measures include securing password storage with salted hashes and using strong encryption. Regular system updates are also essential to patch vulnerabilities.
Why are Brute Force Attacks a Problem?
Anytime you see a story or an industry stat about RDP being involved in a cyberattack, keep in mind that, at the time of the attack, the attacker either did or did not have a working username and password with which to log on.
In scenarios where the attacker is starting from scratch—as with initial access brokers—the goal is to not just gain access but also derive a working credential set that will either be used in the current attack or sold on the dark web to another attacker looking for initial access.
That means that sometimes attackers need to use brute force password attacks to figure out the password associated with a given username.
Brute force attack tools are designed to automate the process of guessing credentials, making it faster and more efficient for attackers.
According to the MITRE ATT&CK Framework (pronounced “ATTACK”) that outlines nearly every malicious tactic, technique, and procedure used by cybercriminals, there are four types of brute force attack methods:
Password Guessing: Systematically guessing passwords using a repetitive or iterative mechanism based on a list of common passwords.
Password Spraying: When an attacker acquires a list of usernames and attempts to log in using the same password for all of them.
Password Cracking: Using rainbow tables or guessing passwords and computing hashes to crack password hashes.
Credential Stuffing: Using credentials obtained from breach dumps of unrelated accounts to gain access to target accounts.
The decision to use one method over another is largely based on whether the attacker knows any usernames and/or passwords on the victim’s network.
But just how prevalent are brute force password attacks?
According to U.K. cyber insurer Hiscox, 17% of the ransomware attacks they saw as part of cyber insurance claims started with a brute force attack. That’s nearly 1 in 5. We’ve also seen brute force attacks en masse in 2022 with 47 million attacks in Southeast Asia targeting remote workers.
So, it’s a very real problem…for numerous reasons.
1. There are Numerous Weak Password Sources
Passwords used in guessing, spraying, or stuffing attacks often come from various sources. One major source is data breaches that expose usernames and email addresses. For example, the May 2016 LinkedIn breach compromised 164 million email addresses and passwords, making it a significant contributor to such attacks.
Another source is pwned databases that catalog commonly used passwords, many of which are surprisingly simple (e.g., “P@ssw0rd!”). Additionally, attackers often exploit targeted guessing opportunities by focusing on specific users, increasing the likelihood of finding weak or predictable passwords.
According to Spycloud’s 2023 Identity Exposure Report, over 7 million of the compromised passwords gathered during breaches involve a love or family theme (e.g., if I know your spouse’s name, I can begin guessing there). These attacks often involve systematically testing various password combinations to exploit weak or commonly used passwords.
2. User Behavior Also Contributes to Security Risks
According to the same Spycloud report, 72% of users in 2022 breaches were reusing previously exposed passwords, with 61% of users in the U.S. reusing passwords.
Passwords are reused an average of 13 times. Part of the reason is the number of systems, applications, and platforms today’s user needs to maintain a logon—in smaller businesses, there are an average of 85 passwords, while in larger businesses, there are only 25.
Using complex passwords can significantly enhance account security, making it more difficult for attackers to succeed in credential compromise efforts.
With computing power today allowing attackers to test as many as 1 billion passwords per second in a brute force attack, password security is essential.
3. Remote Access Can Provide Attackers Ways to Gain Unauthorized Access
Let’s add remote access to the discussion, as brute force attacks are only the means of gaining unauthorized access; the real vulnerability lies in how your hybrid workforce engages with corporate resources.

Some organizations are still (still!) relying on RDP (the protocol that won’t die the horrible cybersecurity death it deserves!). A recent report revealed that cybercriminals abused RDP in 90% of incidents analyzed, making it a critical vector for ransomware attacks. Even if you aren’t using RDP, other remote access applications can also present significant risks—16% of data breaches began with the compromise of RDP or another remote access application.
This means that any method of remote access is an attack vector for cybercriminals. Since 50% of organizations don’t rate themselves highly effective in mitigating remote access risks, it’s crucial to implement stronger authentication measures beyond simple password use to secure remote access effectively.
Prevention Best Practices Against Brute Force Attacks
Preventing brute force attacks requires a multi-layered approach that combines strong policies, technical safeguards, and user education. While multi-factor authentication (MFA) is the foundation of defense. It implements comprehensive strategies to ensure a more active security posture. Here’s how you can stay ahead of brute force attacks:
Establish Robust Password Policies
Strong password policies are the foundation of any brute force prevention strategy. Ensure that all users adhere to these best practices:
Length and Complexity: Require passwords to be at least 12 characters long, with a mix of upper and lower case letters, numbers, and special characters.
Regular Updates: Enforce password expiration policies to limit the window of opportunity for attackers.
Avoid Reuse: Implement systems that prevent users from recycling old passwords.
Ban Common Passwords: Use tools to block weak or easily guessed passwords, such as “123456” or “password.”

Implement Security Monitoring Tools
Real-time monitoring and alerting can help detect and respond to brute force attacks before they succeed. Consider deploying the following tools:
Intrusion Detection and Prevention Systems (IDPS): Tools like Snort or Suricata can detect unusual login attempts and block suspicious activities.
SIEM Solutions: Security Information and Event Management (SIEM) systems like Splunk or LogRhythm centralize log data and provide insights into potential brute force activity.
Account Lockout Thresholds: Configure systems to lock accounts temporarily after a specific number of failed login attempts.
Educate Employees on Security Practices
Human error is a common vulnerability that attackers exploit. Providing ongoing training ensures employees are equipped to recognize and mitigate risks:
Phishing Awareness: Train staff to identify phishing attempts that may precede brute force attacks.
Password Hygiene: Emphasize the importance of unique, strong passwords for both work and personal accounts.
Reporting Protocols: Encourage employees to report suspicious login attempts or system behaviors promptly.
Leverage Technical Configurations
Technical safeguards can make it significantly harder for attackers to execute brute force attacks. Implement these measures:
Rate Limiting: Slow down or block IPs after a series of failed login attempts.
CAPTCHA Integration: Add CAPTCHA challenges to login pages to prevent automated login attempts.
IP Whitelisting: Restrict login access to specific IP ranges, particularly for sensitive systems.
Encrypt Passwords: Use strong encryption algorithms, such as Argon2 for storing correct password hashes.
Remote Access Beyond the Password
Brute force attacks continue to pose significant risks, but a proactive approach and prevention strategies can drastically reduce their impact. By implementing multi-factor authentication (MFA), enforcing strong password policies, and leveraging advanced security tools, organizations can build a robust defense against unauthorized access.
Even if your organization relies on older or more vulnerable remote access methods like RDP, requiring MFA for all logins is a critical first step. Beyond MFA, strategies such as using high encryption rates, salting password hashes, setting login attempt limits, and employing CAPTCHA challenges after repeated failures can thwart brute force attacks before they succeed.
It’s also essential to educate employees, monitor suspicious activity, and deploy tools like intrusion detection systems to identify potential threats in real time. The goal is not just to respond to attacks but to prevent them from materializing.
For those who have read this article to the end, the takeaway is clear: brute force attacks can be mitigated with deliberate, layered security measures. Start with MFA—it’s one of the simplest yet most effective ways to secure remote access and protect your organization. Don’t wait to strengthen your defenses; the time to act is now.