What is remote desktop encryption, and how does it protect remote access sessions?

When you initiate a remote desktop session, what you see on your screen is data traveling between your device and the remote desktop client. Information about what is changing on the screen, what keyboard inputs are being made, and what mouse clicks are being made is sent across the network in real time. If this data is not protected, it could be intercepted or modified by unauthorized people or devices.
Remote desktop encryption is the technology that stops this from happening. It changes every operation into encrypted data that only the sender and the receiver can decrypt. So even if secure communications travel over a public or unsecured network, your data remains confidential and unchanged.
Encryption is one of the most effective ways to protect against data theft or unauthorized remote access. RealVNC Connect uses full end-to-end encryption with Perfect Forward Secrecy built into our protocol. This means the session cannot be decrypted by a man-in-the-middle during the session, and that session data cannot be saved or decrypted later.
Why does remote desktop encryption matter for your business?
Companies must prevent unauthorized individuals with fraudulent or destructive intentions from gaining control of their corporate systems and resources, especially during a remote desktop session or when connecting to a remote computer over the internet.
Not only that, but encryption also helps businesses comply with data protection and industry standards like GDPR, HIPAA, and PCI-DSS. Choosing remote desktop tools with robust encryption ensures you fulfill those obligations and reduces the risk of financial penalties or data breaches.
But encryption is only part of the picture. To see how it works in practice, it helps to understand the systems that carry your data between devices. These are called remote desktop protocols.
What are remote desktop protocols?
Remote desktop protocols are sets of rules that govern data transfer between two computers. They define how changes on the screen, keyboard inputs, and mouse actions are sent. To securely and efficiently carry out this communication, each remote access tool uses its own protocol.
The device’s performance and security can be influenced by the protocol you choose. For instance, some protocols might be designed for speed, while others are designed for compatibility or encryption strength. Understanding the differences will help you choose the most appropriate solution for your working environment.
VNC and the RFB protocol
Virtual Network Computing (VNC) was created by the original founders of RealVNC. The technology is based on the Remote Framebuffer (RFB) protocol, which enables one computer to control another by sending screen updates and input commands.
Modern versions of RealVNC Connect extend this foundation with advanced encryption, multi-factor authentication, and cloud connectivity. Every connection is encrypted end-to-end using AES standards, and no direct exposure of ports or IP addresses is required.
Because RFB is platform-independent, it supports secure access across Windows, macOS, Linux, and other systems without additional configuration. This flexibility makes VNC suitable for both enterprise environments and smaller organizations that need secure, straightforward remote access, as well as for those that want to support remote work.
RDP (Remote Desktop Protocol)
One of the most widely accepted standards for remote access is the Remote Desktop Protocol (RDP), designed by Microsoft, which is mainly targeted at the Windows environment. RDP employs Transport Layer Security (TLS) to enhance the privacy of the link between the client and the server.
Although there is encryption in RDP, its security is strongly dependent on the right configuration and regular maintenance. RDP ports left open are often targets of brute-force attacks and ransomware. Weak passwords, outdated systems, or outdated settings can make a network susceptible.
Among the measures that administrators can take to improve RDP security are the following:
- Using Network Level Authentication (NLA) to verify users before the establishment of sessions
- Limiting access only to trusted devices and user groups
- Instead of exposing RDP ports directly to the internet, use a VPN or RDP gateway
Even when IT teams take these precautions, RDP still faces risks associated with listening ports and exposure to legacy protocols. Modern encrypted remote access solutions avoid these risks by never exposing a direct listening interface to the internet.
Why protocol choice matters
The decision on which remote desktop protocol to use ultimately affects the session’s effectiveness and security level. Some of the concerns that determine encryption strength, authentication methods, and network exposure all stem from that decision.
RDP might be the best option for closed, internal environments. But in public or mixed networks, RFB-based solutions such as RealVNC Connect offer a higher level of security due to their zero-trust design.
Organizations that want to keep their networks safe without compromising the ease of use can do so by using a secure protocol combined with end-to-end encryption.
Choosing a secure protocol is critical, but it’s only part of the equation.
The type and strength of encryption used during remote sessions also influence how well your data is protected from interception or tampering. That’s where encryption levels like 128-bit or 256-bit AES come into play.
Different levels of encryption
There are different levels of encryption that vendors refer to in their specifications, such as 128 or 256-bit AES (Advanced Encryption Standard), which reflect the algorithm used to protect the data and how hard it is for an attacker to break in (128 or 256-bit).
In simple terms, 256-bit AES provides a higher level of security than 128-bit AES, which offers stronger protection for sensitive data. Both are considered secure, but the longer the bit length, the more time and computing power it would take to break them.
The mathematics behind data encryption
Encryption is a mathematical algorithm that protects data transmitted between two devices (end-to-end) during a remote access session, ensuring it remains unreadable to anyone trying to gain unauthorized access through weak points in the network. The key to this lock is a secret number known only to the sender and receiver, which changes with each session.
The level of encryption reflects the number of possible key combinations. The more bits of encryption, the more possible keys there are, so the more difficult it is to compromise the encryption.
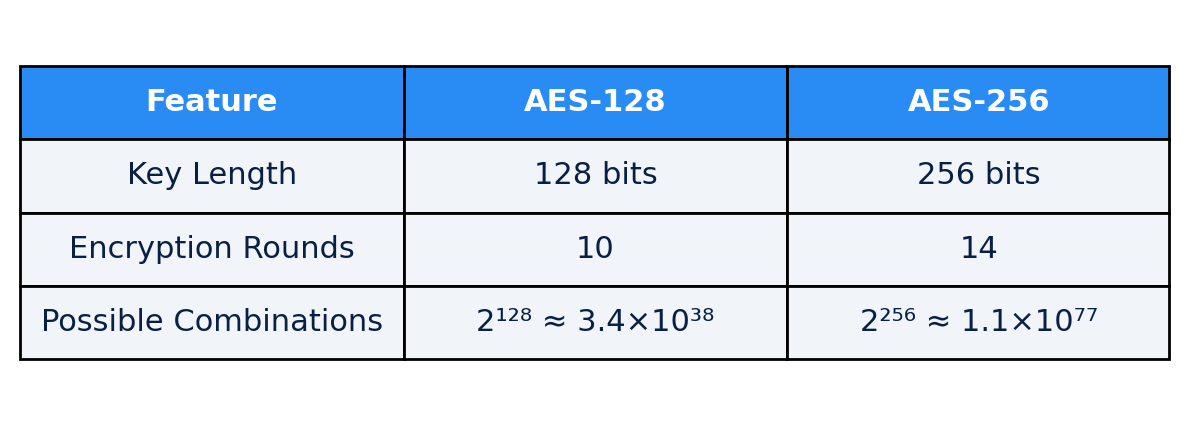
A 128-bit level of encryption has 2128 possible key combinations (340,282,366,920,938,463,463,374,607,431,768,211,456 – 39 digits long), and 256-bit AES encryption has 2256 possible key combinations (78 digits long).
Based on how the math works out, 256-bit encryption is not twice as hard to break into or ‘crack’ as 128-bit encryption, but 340 billion-billion-billion-billion times harder.
How long would it take to crack remote desktop encryption?
Cracking either of these encryption levels would be extremely time-consuming, given the total number of possible key combinations and the current state of computer processing power.
‘Extremely time-consuming’ is in fact a gross understatement. Even if you build a worldwide network of supercomputers designed just for the purpose of trying combinations as fast as possible, it would still take more than 100 billion years on average to stumble on the right one. For comparison, the universe has only been around for 13.8 billion years.
This also assumes that you could afford the astronomical energy bills required to run the system for that long—a significant fraction of the planet’s total energy use each year for 100 billion years. A 256-bit key would be 340 billion-billion-billion-billion times as impossible.
Why a 512-bit encryption level isn’t always better
So why are some vendors starting to promote 512-bit encryption? They rely on busy people assuming that 512-bit is ‘twice as good’ as 256-bit. However, the original AES standard only specified 3 key sizes: 128, 192, and 256 bits.
These key sizes have been proven to be cryptographically secure, so although 512-bit AES could be theoretically created, it wouldn’t be tried and tested.
They may argue that as processor technology advances, it becomes more feasible to crack existing levels of encryption. Until we see widespread adoption of cheap, powerful, and reliable quantum computers, we cannot even begin to contemplate such a scenario, which is why most experts agree that 128 and 256-bit AES encryption are sufficiently complex to remain extremely robust for many years to come.
How to choose the right level of encryption for remote desktop connections
So after all this explanation, which level of encryption is appropriate for your specific environment? The answer depends on your environment’s needs, but one very important point is that encryption is essential. Choosing the right encryption level also depends on whether you’re using a private network, RDP gateway, or connecting through a virtual private network (VPN) for added protection.
Common mistakes to avoid
Be aware that free, open-source remote access software is available that provides no encryption by default. Using unencrypted remote access software within a business environment is simply a bad idea, since it allows anyone to view and modify your remote control session, without any indication of it occurring.
Unencrypted software can also allow attackers to gain unauthorized access, hijack sessions, or perform credential theft through weak passwords and older versions of software.
The price you will pay for a commercial remote access software subscription is minor compared to the risks you will introduce to your business by using a “free” unencrypted product. A single successful attack could cost your business tens of thousands of dollars in compromised bank accounts, lost data, blackmail, or reputational damage. Don’t take this risk.
Choosing the best level for your needs
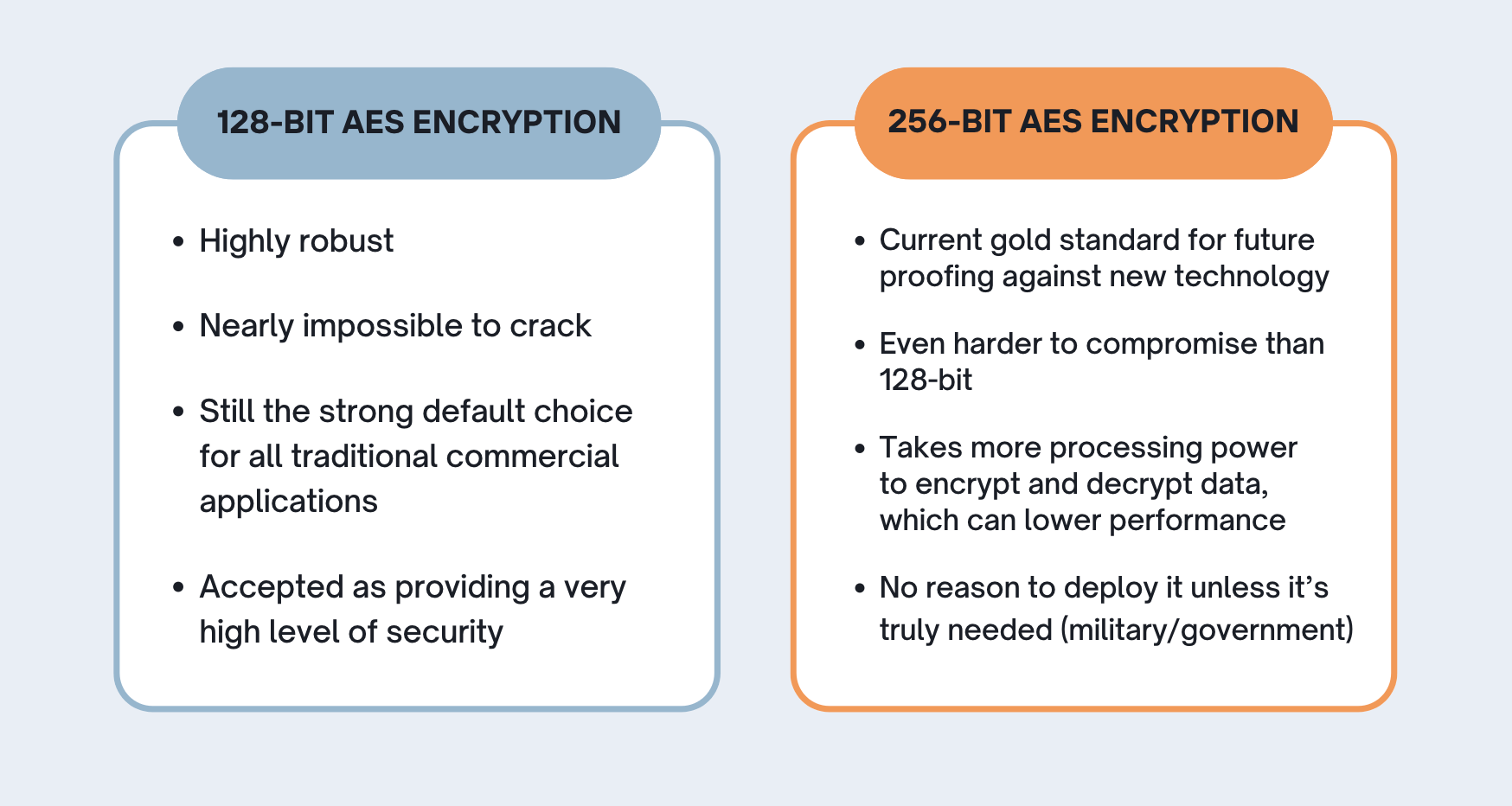
As you can see, 256-bit encryption is sufficient to protect against sustained attacks from highly sophisticated criminal gangs or the resources of rogue state entities. Given the quality of this level of encryption, it is often mandated by standard bodies associated with the financial, medical, and security industries.
In particular, it’s considered safe enough to protect TOP-SECRET classified information. You should insist on 256-bit AES encryption if you have very high security requirements or if it is specified in an industry-standard.
So, what’s the verdict?
End-to-end data encryption is essential for any commercial remote access software deployment. In combination with additional security features such as multi-factor authentication and controlled teams and groups, you can create a highly secure remote access strategy.
The decision between 128-bit and 256-bit AES encryption for remote desktop connections must be made on a case-by-case basis, and the answer largely depends on the sensitivity of your data and the requirements and standards set by your industry.
Additional ways to secure remote desktop access
Of course, whichever level of encryption you go for, it’s not the only thing to consider when ensuring your data stays safe during a remote desktop session. Making sure you have unique passwords, staying off public Wi-Fi, and keeping track of your old accounts all contribute to your overall security.
If you are interested in learning more, read our Remote Access Security Checklist.
How RealVNC Connect keeps your remote desktop services secure
RealVNC Connect protects every session with end-to-end AES-GCM encryption up to 256-bit. With Perfect Forward Secrecy, even if a key is compromised, past sessions stay secure. RealVNC never stores your passwords or session data, so your access always stays private. Ready to experience secure remote access? Download RealVNC Connect today and try it free for 14 days.







