You’d think remote access was a non-issue today; even after the need to utilize easy remote access during the pandemic, the continued misuse of externally facing remote access over the last three years should serve as enough of a lesson that insecure remote access (whether Microsoft’s basic RDP or otherwise) should be nonexistent in today’s networks.
But that’s just not the case. In short, insecure remote access is alive and well.
To make the point, I wanted to take the time to look at a few pieces of industry research that highlight the continued existence of the problem of insecure remote access, as well as how remote access is being misused.
We all are aware that ransomware is the more prevalent and pervasive type of cyberattack today. For example, these kinds of attacks are so damaging that the U.S. Government’s Cybersecurity & Infrastructure Security Agency (CISA) continually puts out advisories on specific ransomware variants – such as the advisory covering Royal Ransomware earlier this year.
Remote access plays a role in many of these attacks (e.g., the attackers behind Royal themselves used RDP as the initial attack vector in 13% of their attacks). But there are many other examples of industry data pointing out the use of remote access.
- According to this year’s newly-release Verizon Data Breach Investigation’s Report, just above one-quarter (28%) of ransomware attacks that involved system intrusion included the use of desktop sharing software.
- Additionally, according to cybersecurity vendor Fortinet, in 51% of ransomware attacks, the exploiting of remote desktop protocol was involved – this is a very real problem today.
So, how is this remote access being leveraged by threat actors? In many cases, it serves as the initial access for attacks (as shown in the Fortinet data). The availability of remote access is so prevalent that, according to cybercrime monitoring and analysis vendor KELA, the most common type of access offered by initial access brokers was RDP (Remote Desktop Protocol) accompanied by compromised credentials.
I think it should be mentioned that I see a lot of industry data focused on RDP (that is, Microsoft’s remote desktop protocol). In general, I feel like the reports are more trying to make the point that externally-accessible remote access (from any software vendor) should be grouped under the umbrella of “remote desktop protocol”, and that this isn’t just a bashing of RDP specifically.
The problem here is that organizations of all sizes continue to enable their remote workforces with remote access solutions (again, RDP and otherwise) that are focused more on productivity than on security, putting the organization at risk; 75% of security experts believe that remote/hybrid work actually increases the risk of cyberattacks, citing the reliance on remote connectivity as a contributing factor.
Not Just Remote Access, but Secure Remote Access
Assuming we’re not going to get away from having remote workers needing to access corporate resources remotely for the foreseeable future, it’s imperative that the remote access solutions used actually improve the security stance of the organization. So, what does that look like? Let’s use some of the current data points made here to outline the future of your secure remote access.
- No externally-facing RDP. Period. Threat actors are well-aware of how to scan for and open RDP session (even if you change the port address). So, unless you put security controls around RDP, it can’t be your solution to enable remote users to access the corporate network. Otherwise, it’s apparent from the data above, it will also end up helping threat actors too.
- No internal RDP either. This isn’t an RDP hate-fest; this is really about the insecurity of the default remote desktop services. There are no real security controls except for the requirement for a username and password – and that’s not enough. Given the data above outlines how RDP seems to be the remote access focus for most threat actors, it makes sense that – if nothing else – stop helping the bad guys by leaving it enabled even internally, as it only helps lateral movement.
- Put secure remote access in place. This goes for both external and internal access purposes. What makes remote access secure is the layers of controls put in place that ensure the correct person is using the correct credential to access only the approved systems with the exact sanctioned level of permissions. So, the types of controls necessary would equate practically to:
- Multi-factor authentication – go beyond username/password combinations and make certain the user of a credential is also its owner.
- Granular Access – your remote access solution has the potential to allow a user to access just about any system. So, there should be some level of control over which users can gain access to which systems.
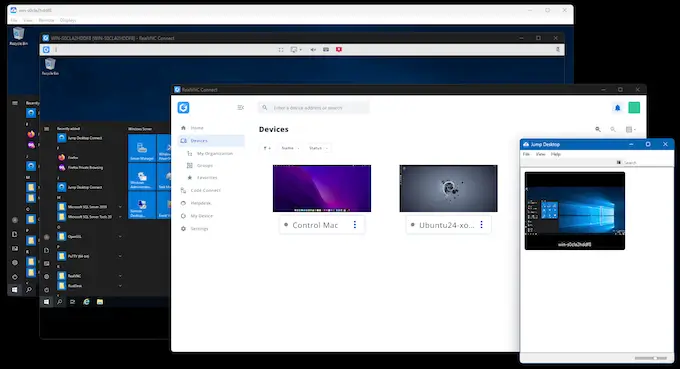
- Centralized Control – the same solution used to enable remote workers to access the corporate network should also enable sanctioned users within the network to remotely access systems within the network. This way you can centrally establish policies, perform deployments, and control remote sessions all from a single solution.
The use of remote access solutions in cyberattacks isn’t going to be going anywhere anytime soon; the bad guys need to access systems in the same way you do so they can perform the same kinds of actions… they just do it with malicious intent. So, the goal here is to maintain the spirit of remote access (enabling users to be productive and get their work done remotely – whether than be internally or externally) but do so in a way that doesn’t assist the threat actor by using a solution without any kind of security controls in place.
And the only way to really accomplish this is to acknowledge the risk remote access creates and make certain that the solution used by remote workers and IT alike is one that enhances the organization’s security while also elevating its productivity.